Article
SSL certificate chain resolver
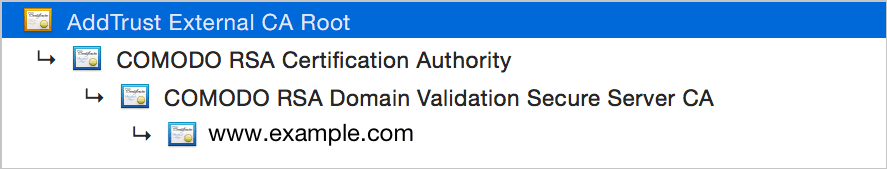
When you purchase an SSL certificate from a certificate authority, in most cases it is signed not by the root certificate of this authority, but by an intermediate certificate(s). The path from your certificate through those intermediates and up to the root is called a certificate chain. While browsers can resolve those chains by downloading certificates from sources specified in them, the whole chain except for the root cert is better to be included in the response your server sends during TLS connection.
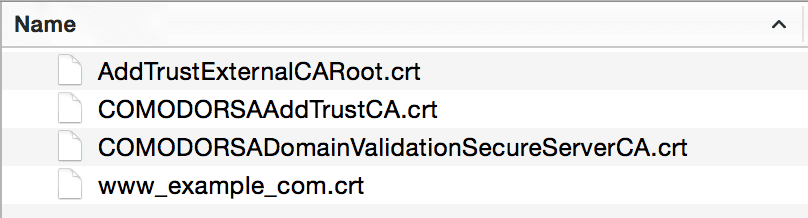
Certificate authorities usually tell you which intermediate certs you should include. For example, here's what COMODO sends to you when you purchase a PositiveSSL certificate:
 To install them on your server, you'll have to concatenate the chain in the proper order. The result should look like this:
To install them on your server, you'll have to concatenate the chain in the proper order. The result should look like this:
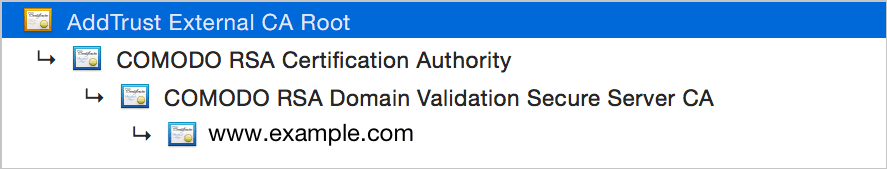 (Note that the root certificate should not be in the concatenated chain, as it is already included in the browser's root CA store.)
(Note that the root certificate should not be in the concatenated chain, as it is already included in the browser's root CA store.)
Note that as of this writing The OS X issue has been fixed)
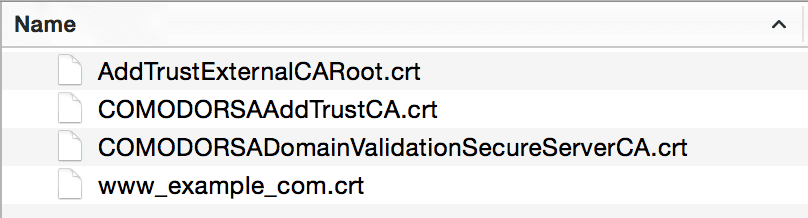 To install them on your server, you'll have to concatenate the chain in the proper order. The result should look like this:
To install them on your server, you'll have to concatenate the chain in the proper order. The result should look like this:
 (Note that the root certificate should not be in the concatenated chain, as it is already included in the browser's root CA store.)
(Note that the root certificate should not be in the concatenated chain, as it is already included in the browser's root CA store.)
The Script
cert-chain-resolver is a little script that will download and concatenate in the proper order the certificate chain for you, given the certificate.Installing cert-chain-resolver
The script is available from GitHub. You can download it using the browser or withwget utility:
wget https://github.com/zakjan/cert-chain-resolver/archive/master.zip
git to fetch the repository:
git clone https://github.com/zakjan/cert-chain-resolver.git
Using the SSL certificate chain resolver script
After you received your certificate from CA, run:./resolve.sh input.pem output.pem
resolve.sh doesn't work in OS X Yosemite — there is an open issue about it, which I hope will be fixed soon.